How IAM policy drift creates security blind spots
Key Takeaways
IAM policies fail during translation across five layers: global policy → internal standards → system implementation → roles → effective access. Each layer introduces interpretation that creates drift over time.
Layered permissions create "toxic combinations" where individually compliant access grants combine into unintended security blind spots - like temporary assignments that persist permanently.
Policy Mesh restores visibility by tracing policy intent through to effective access, enabling organizations to detect drift and lateral entitlement movement before it becomes a breach.
Where IAM policy and access begin to drift
I've often found that layering of enterprise policies - and the identity and access management (IAM) permissions that represent them across systems, directories, and apps, becomes increasingly risky and difficult to visualize and reason about over time.
This chain of translation, basically the link between high-level policy and the technical permissions that represent them, is where enterprise security begins to fracture. It's not just about one bad decision; it's about how the links in that chain diverge over time.
It's how iterative decisions accumulate: Joiners, Movers, Leavers, system changes, new systems, business evolution and regulatory expansion. Each change aligns with policy at the time. But the combination, over time, creates a compounded effective access state that no single policy review ever saw in full.
And, as those decisions stack, precision can degrade. Not because people are careless or governance doesn't exist. We lean into our guardrails and make judgments within our assigned scope. But the governance mechanisms that built the chain rarely have a clear way to map effective access - the sum of all those translations—back to the original policy intent.
What we're often missing isn't another policy document or another review cycle. It's a connective layer - what I've started calling a Policy Mesh - that helps us see how intent actually plays out across the Chain of Translation over time.
The chain of translation: How policy becomes practice
If we simplify it, the link between high-level intent and technical execution usually looks like this:
Global policy & intent: Driven by frameworks like GDPR, CCPA, or DORA, this defines the "What" (e.g., "Protect regional data from unauthorized access").
Internal standards & requirements: The global intent is interpreted into company-wide rules, such as having geo-location based access controls for any EU-based data domain.
System-specific implementation guidance: Technical architects translate those standards into platform-specific instructions, such as how to configure AWS Service Control Policies or Azure Management Groups.
Roles, groups, & permission sets: These are the actual configuration objects created within a system. At this stage, the original intent is often several layers removed, replaced by technical labels like Finance_Analyst_EU_Read.
Effective access & control behavior: This is the final, "resolved" state - what an identity can actually do once all previous translations have stacked together.
How temporary assignments create permanent access risks
While each individual link in this chain is usually reasonable and aligns with policy, the friction lives in how these layers interact over time. Consider Alex Morgan ('Example User'), during a temporary regional assignment and the desire to enable him to support his home team and give him access to US data domains:
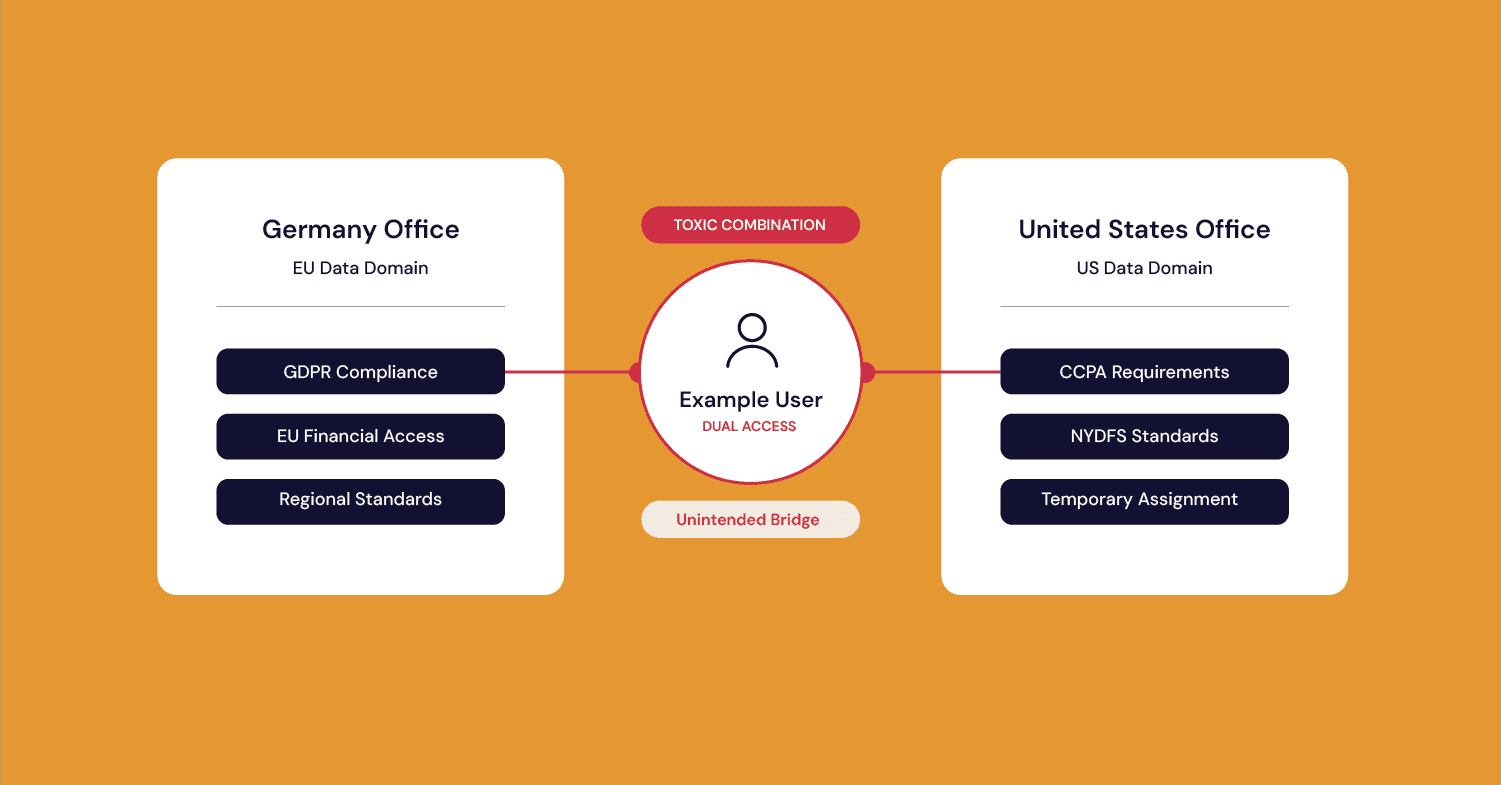
The initial chain: In his home office in Germany, Alex's access is governed by GDPR and internal privacy standards (e.g., geo-location based access controls).
The layered change: During a six-month assignment to the US, new links are added to his chain: CCPA, NYDFS, specific US financial system requirements, and temporary exemptions from geo-location-based access controls.
The fracture: Because the move is temporary, these two chains are layered rather than replaced.
The resulting entropy: When Alex is in the US, he has access to both EU and US data domains. When he returns to Germany, some of those US layers inevitably persist to continue supporting him work with the US team.
This isn't out of negligence - he needs to continue supporting both teams and now he continues to have access to both data domains. However, because the governance cycles that built the chain rarely have a mechanism to deconstruct or "right-size" the layers once they've been compounded, we are left with a permanent bridge between two sensitive regions. The individual permissions are still "valid," but the resolved access has become a toxic combination that exists outside of a single, unified policy intent.
The cumulative effect is that Alex's access is now technically compliant with two separate policies, and it is architecturally inconsistent with the enterprise's broader risk appetite. It is the accumulation - across regions, systems, and time - that makes the effective access harder to reason about with clarity.
The real problem isn't IAM policy - it's translation
In my experience, the breakdown isn't usually the policy itself; it's the entropy that sets in as that intent is translated down into the weeds of technical configuration.
Most organizations operate with multiple layers of policy: global security policy, privacy and data handling obligations, regional overlays, business-unit standards, system-level requirements. These layers are necessary. And every layer introduces interpretation.
Over time, interpretations diverge. Two systems implement the same requirement differently. A role built years ago remains even as responsibilities evolve. Exceptions accumulate because removing access can feel riskier than leaving it in place - and because other priorities inevitably take over.
We make reasonable decisions based on experience and context. We lean into governance cycles knowing they won't be perfect. But without continuous visibility into how policy maps to effective access, we eventually lose confidence in whether the current state still reflects the original intent.
What the Policy Mesh actually is
When I talk about a Policy Mesh, I'm not describing a new universal control plane. I'm describing a translation and traceability layer - a way to maintain living connections between:
Policy intent
Derived standards and requirements
System-level implementation
Roles, groups, and permissions
The effective access they create
It's a mesh because these relationships aren't linear. Policies overlap. Requirements fork. Roles intersect. Access permissions combine across systems.
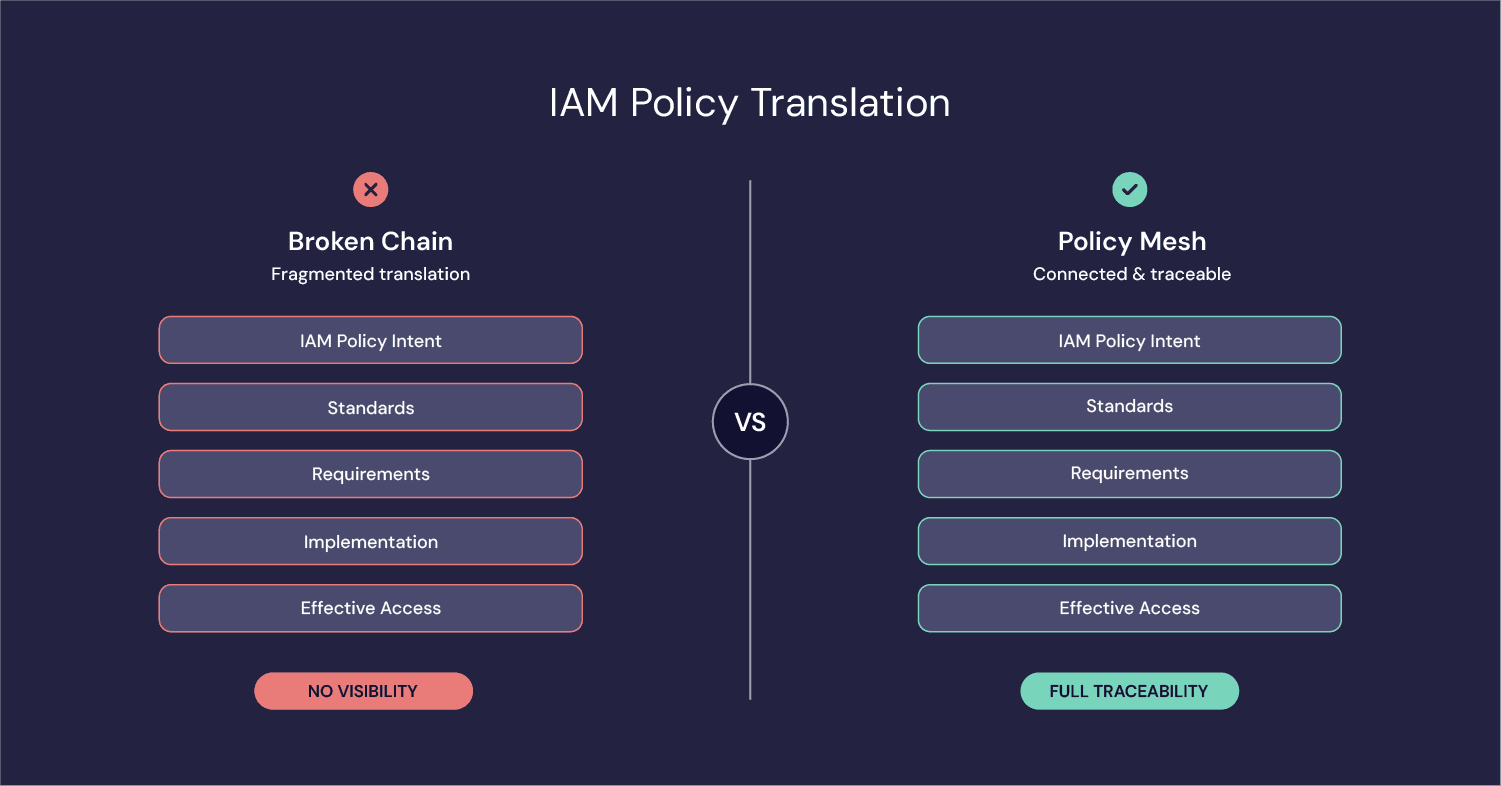
The goal isn't to eliminate policy layers or magically resolve contradictions. That's not realistic. It's to make those relationships visible, traceable, and easier to reason about during everyday change and during governance and review cycles. When that translation is visible, we can move from debating policy in meetings to managing it operationally.
The hidden risk of lateral entitlement movement
One place this layered complexity becomes visible is in lateral entitlement movement.
We often evaluate access permissions one decision at a time - approving a role here, granting a group there, extending access for a reasonable business need. Each change may be implemented by different groups and comply with policy and pass review.
But over time, those permissions stack. An inherited role, a legacy group, or a service account tied to multiple systems creates a toxic combination. As we see with Alex Morgan, these aren't always "errors"; they are often the intersection of two legitimate permissions that, when combined, create a pathway that no single policy intended.
These circumstances can result in lateral account movement - where access in one system may create pathways into another, sometimes allowing someone to operate around the intended constraints of a separate account or gain unintended reach across systems.
Attackers don't rely on a single catastrophic permission; they chain together the layered ones we've accumulated. This isn't about a single misconfigured role. It's about compounded effective access.
A Policy Mesh helps surface those chains - not by replacing governance, but by making layered access relationships easier to see and reason about for analysts, administrators, compliance and auditors, before someone else exploits them.
Where AI actually changes the equation
Traditional governance tooling manages roles, approvals, and certification cycles well. It can confirm that a role was approved or flag separation-of-duties violations. What it struggles with is compounded interpretation - understanding how multiple policy translations intersect across systems and time.
This is where I believe AI can materially shift the equation - not by replacing governance, but by maintaining and making visible the connective tissue between policy intent and layered implementation.
AI can help:
Trace which regulatory obligations influenced each granted role
Map how inherited roles and temporary assignments combine into effective access
Detect when layered permissions enable lateral entitlement movement across systems
Surface when compounded access diverges from peer baselines
Visualize an approximate effective blast radius - showing how access expansion meaningfully shifts reach across users, systems, networks and data domains
In large enterprises, lifecycle events happen at scale. Manual review cycles struggle when velocity increases and compounded access patterns evolve faster than humans can correlate them. At that scale, compounded access patterns can quietly enable lateral entitlement movement long before anyone sees the full chain.
AI can meaningfully shift that conversation by allowing visibility and correlation to operate at the same scale and speed as change itself. This doesn't eliminate ambiguity, and it won't perfectly model intent - but it can surface drift earlier than humans can at velocity and scale.
What this ultimately helps us see more clearly is Effective Access - not the individual roles that were approved, but the compounded access state that emerges when layered permissions interact across systems and time.
How to start without re-architecting everything
If this resonates, the instinct might be to look for a broad architectural overhaul. In my experience, that's rarely where sustainable progress begins. The pattern that tends to work is more disciplined: identify discrete use cases that matter, and use them to establish and strengthen the strategic architecture and foundations over time.
A more realistic starting point is a contained, high-value domain - for example, a core financial reporting application used for quarterly adjustments and regulatory reporting. In that environment, the policy overlays are relatively clear. Financial controls are defined. Elevated permissions are periodic and predictable. Ownership is established. Review cycles already exist. The blast radius is understandable.
And yet, even here, translation drift can accumulate. Privileged roles may be granted standing access because it's easier operationally. Temporary adjustments may layer rather than replace existing permissions. Over time, the effective access model can become more expansive than intended—not through negligence, but through iteration.
This is where the Chain of Translation can be strengthened deliberately. Map policy to requirements. Requirements to controls. Controls to roles. Roles to permissions. Permissions to users. Make those relationships visible. Surface layered combinations and clarify what effective access actually looks like in practice.
In a bounded financial reporting stack, that work is manageable. It builds discipline without requiring enterprise-wide re-architecture. From there, organizations have options. They can extend the same translation clarity into adjacent systems, replicating the pattern horizontally. Or they can deepen it within the original domain by introducing more dynamic access patterns—narrowing elevated windows and refining standing privilege.
In either direction, maturity spreads from proof, not aspiration. Each focused use case strengthens the enterprise fabric—policy models, access standards, governance muscle, and technical architecture - in ways that make broader evolution possible. For more on building this foundation, see our previous article on why IAM policy management is broken.
Making policy translation visible and manageable
Policy has always been about intent, and identity has always been about execution.
The friction has never really been about writing better policies or building more sophisticated role structures. The friction is in the translation—in maintaining the visible connective tissue between policy intent and the technical configurations that are supposed to represent it.
When that translation is visible and traceable, we shift from reactive governance to operational management. We move from debating what policy should be to managing what it actually is. And in doing so, we make it possible to adapt governance and access models to the velocity and complexity of the organizations we're trying to protect.
Erik is an cybersecurity executive and advisor with over 20 years of experience leading cloud security, identity, and enterprise risk transformation. Formerly SVP – Cloud Security & Architecture at M&T Bank, he has also held leadership roles at GitHub, Veracode, and ACV Auctions. Erik advises emerging cybersecurity innovators, including Cyera, Legit Security, Cyberstarts, and Permiso Security, and through his firm, Pragmatic Strategies, helps organizations turn complex security challenges into actionable strategy and measurable results.